About Encrypted Direct Messages
X seeks to be the most trusted platform on the internet, and encrypted Direct Messages are an important part of that. As Elon Musk said, when it comes to Direct Messages, the standard should be, if someone puts a gun to our heads, we still can’t access your messages. We’re not quite there yet, but we’re working on it. Until then, here is the Encrypted Direct Message we are releasing - a new way of communicating on X that will appear as separate conversations, alongside your existing Direct Messages in your inbox.
How does it work?
The latest version of X apps (iOS, Android, Web) generate a pair of device specific keys, called private and public key pair. The public key is automatically registered when a user logs into X on a new device or browser; the private key never leaves the device and therefore is never communicated to X. In addition to the private-public key pairs, there is a per conversation key that is used to encrypt the content of messages. The private-public key pairs are used to exchange the conversation key securely between participating devices.
We employ a combination of strong cryptographic schemes to encrypt every single message, link, and reaction that are part of an encrypted conversation before they leave the sender’s device, and remain encrypted while stored on X’s infrastructure. Once messages are received by the recipient devices, they are decrypted so that they can be read by the user.
We aim to open source our implementation and describe the technology in depth through a technical whitepaper later this year.
Who is eligible to send and receive encrypted messages?
Users need to satisfy the following conditions in order to send and receive encrypted messages:
- both sender and recipient are on the latest X apps (iOS, Android, Web);
- both sender and recipient are verified users or affiliates to a verified organization; and
- the recipient follows sender, or has sent a message to sender previously, or has accepted a Direct Message request from the sender before.
How to send encrypted messages?
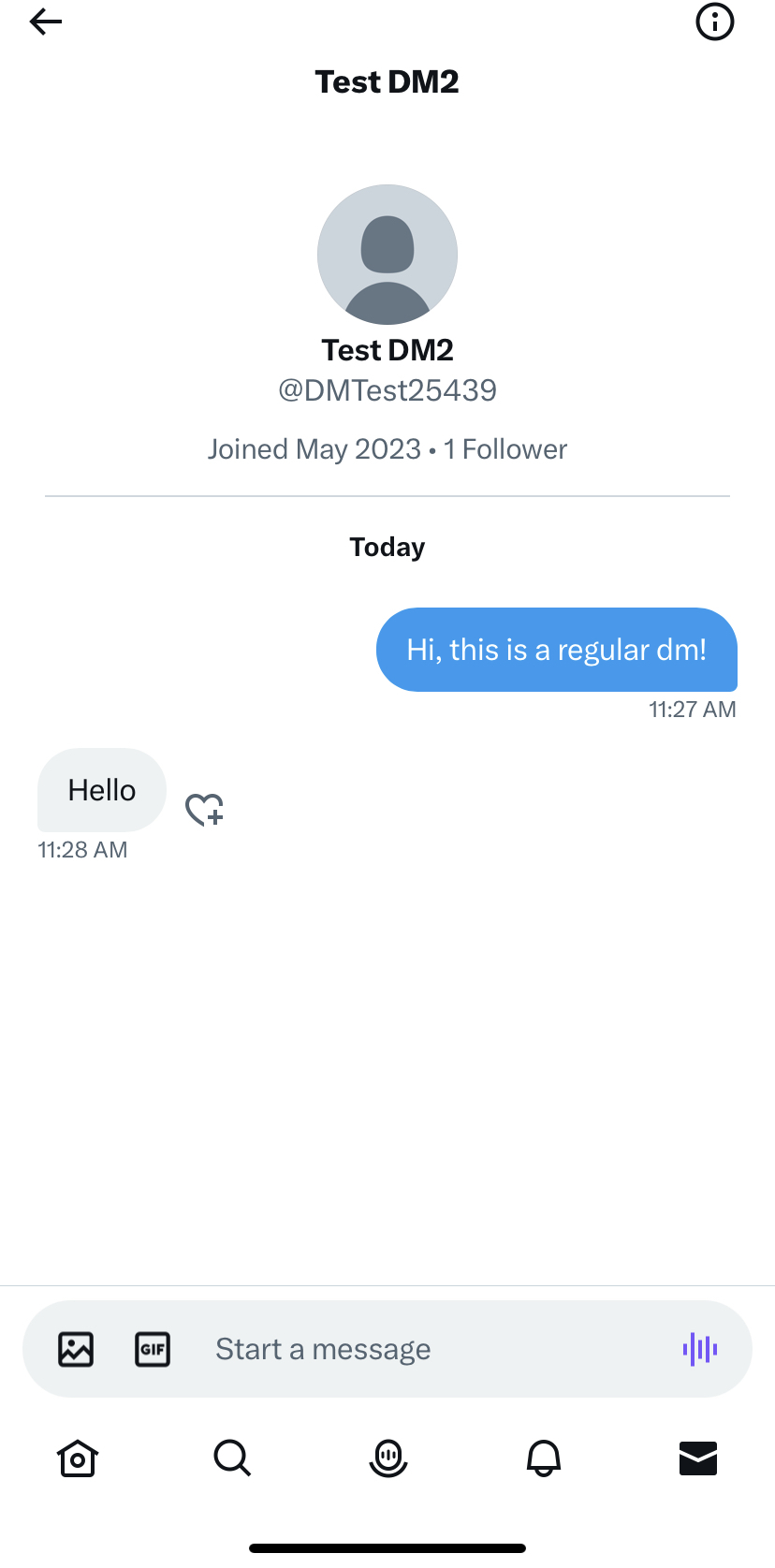
Sending an encrypted message is similar to sending a regular unencrypted message. If you are eligible to send encrypted messages, you will see a toggle after clicking on the message icon to enable “encrypted” mode. Selecting an eligible recipient, composing a message and clicking Send will send an encrypted message.

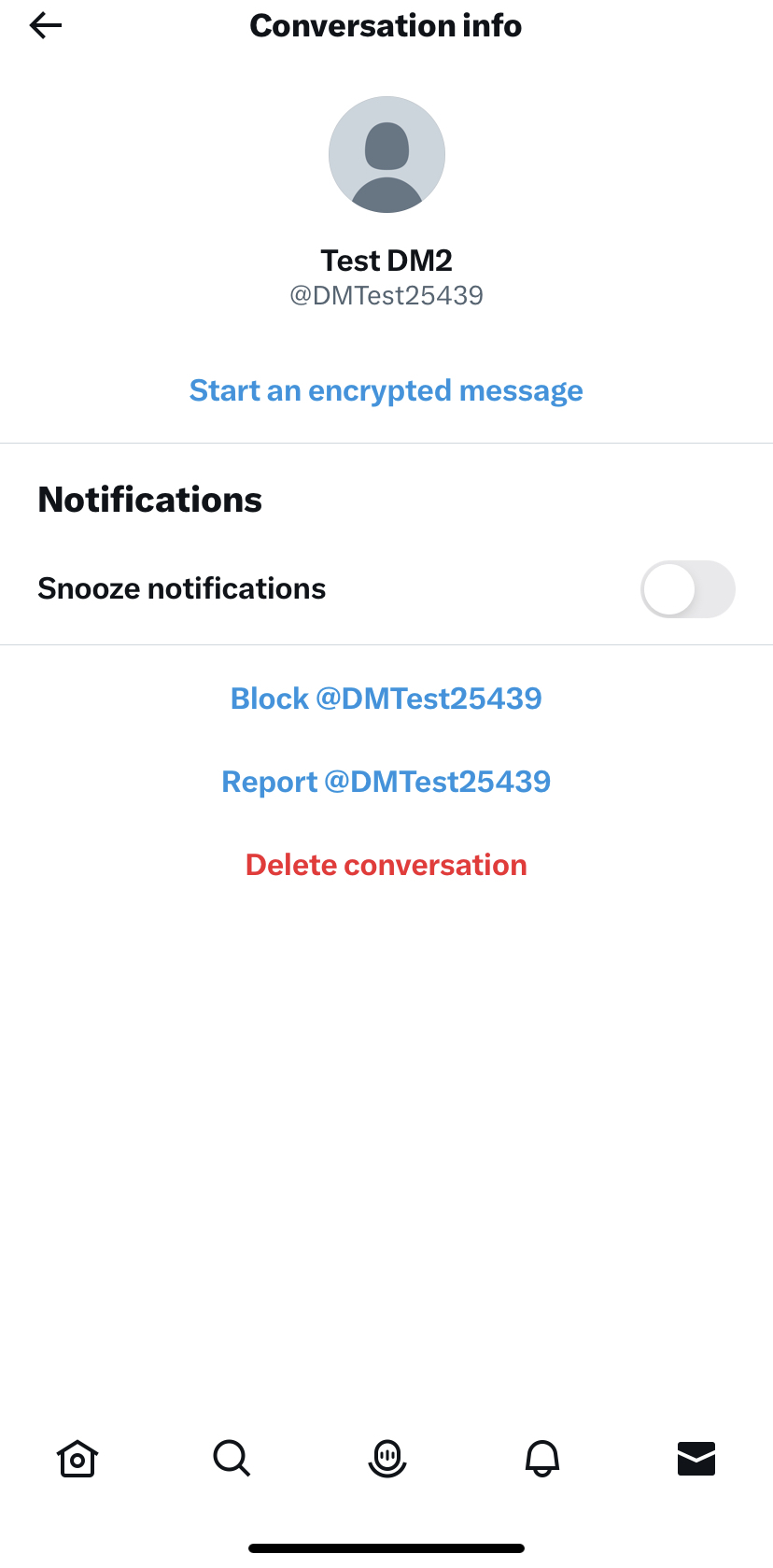
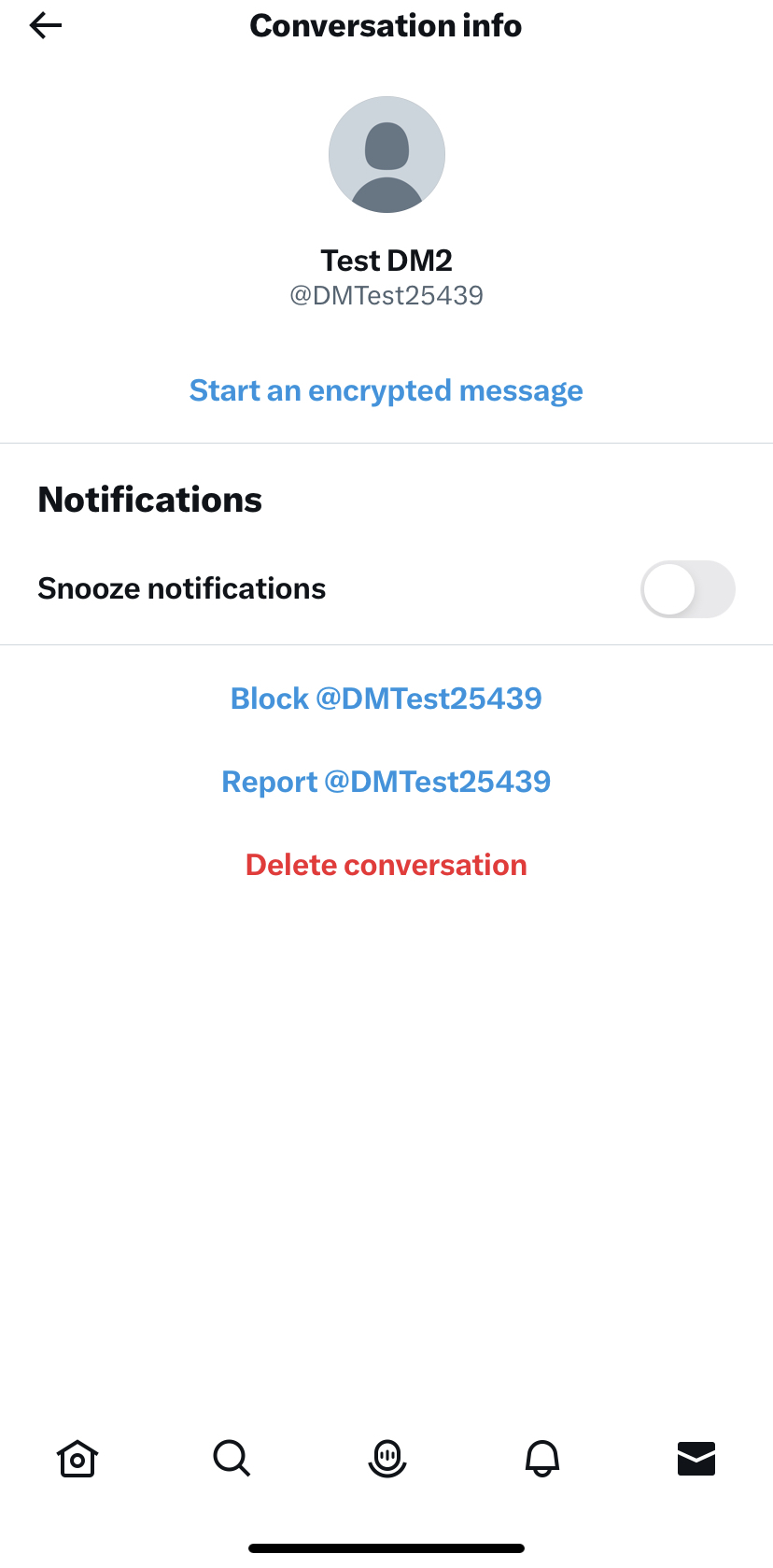
Alternatively, you can send an encrypted message through the conversation settings page of an unencrypted conversation:
- Tap into an unencrypted conversation from inbox.
- Tap on the information icon .
- Select Start an encrypted message.
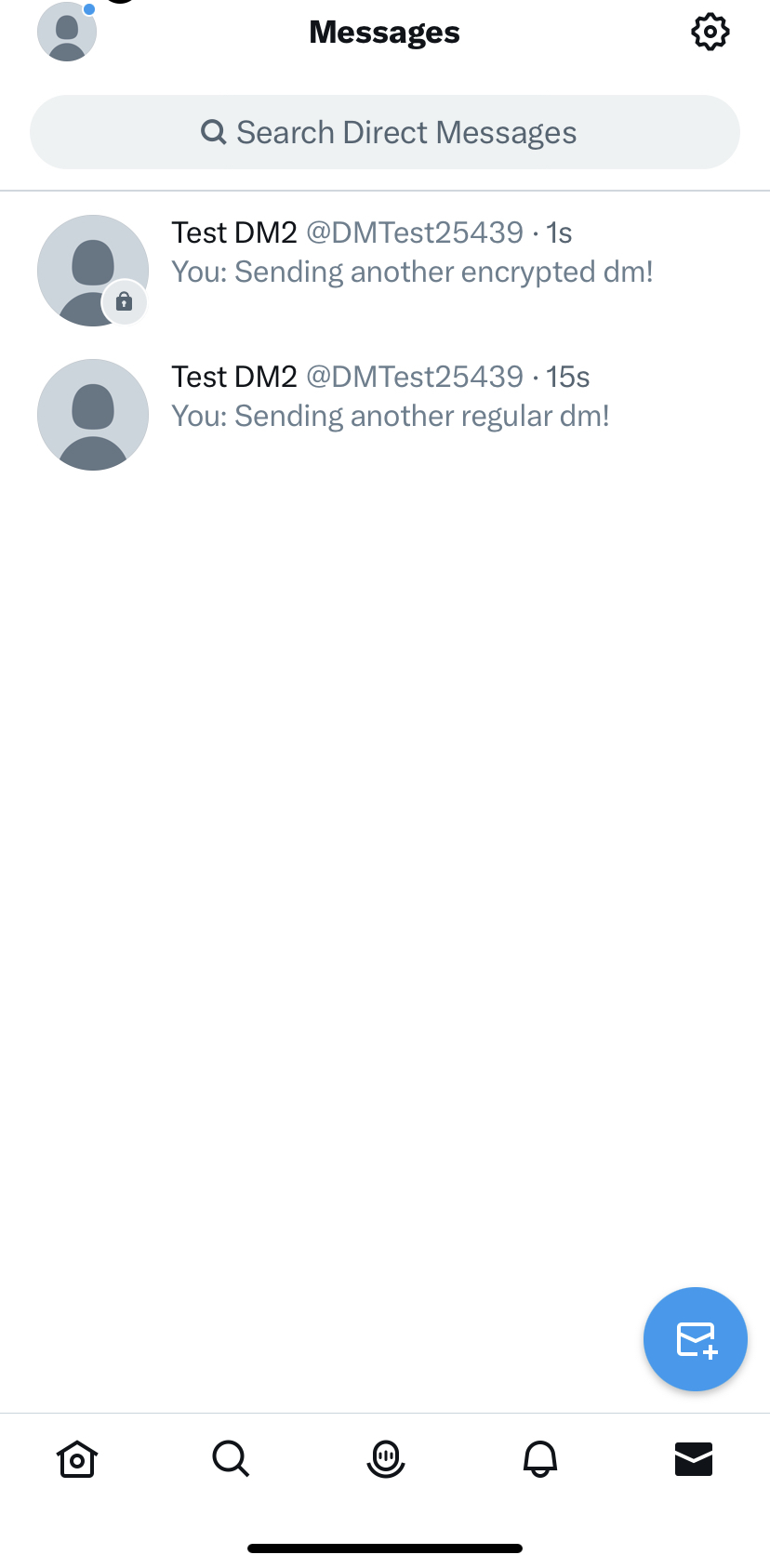
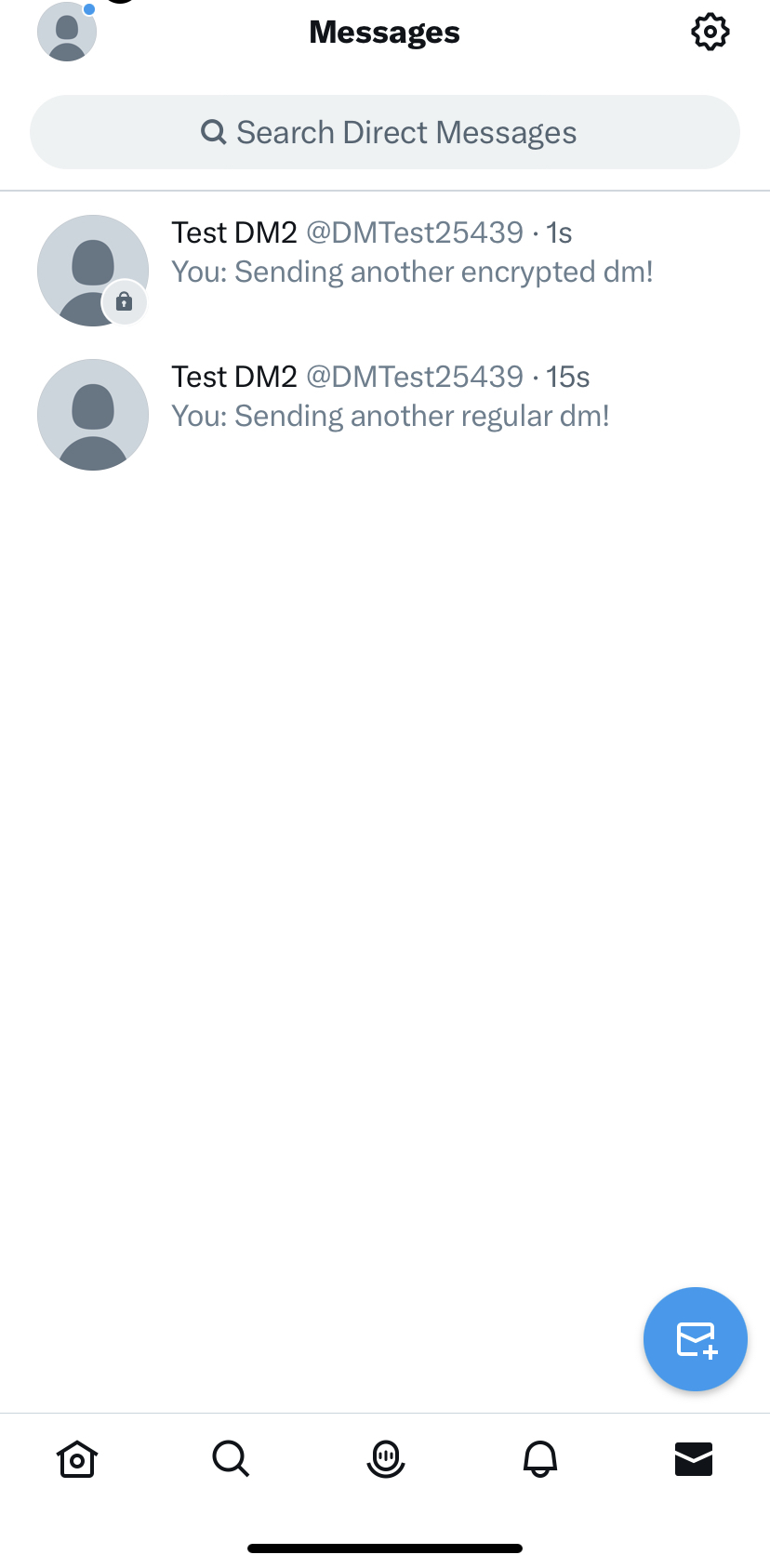
Differentiating between encrypted and unencrypted conversations
Encrypted conversations are visually differentiated from unencrypted conversations through a lock icon badge on the avatar of the user you are talking to. The badged avatar shows up in both the inbox and conversation views.
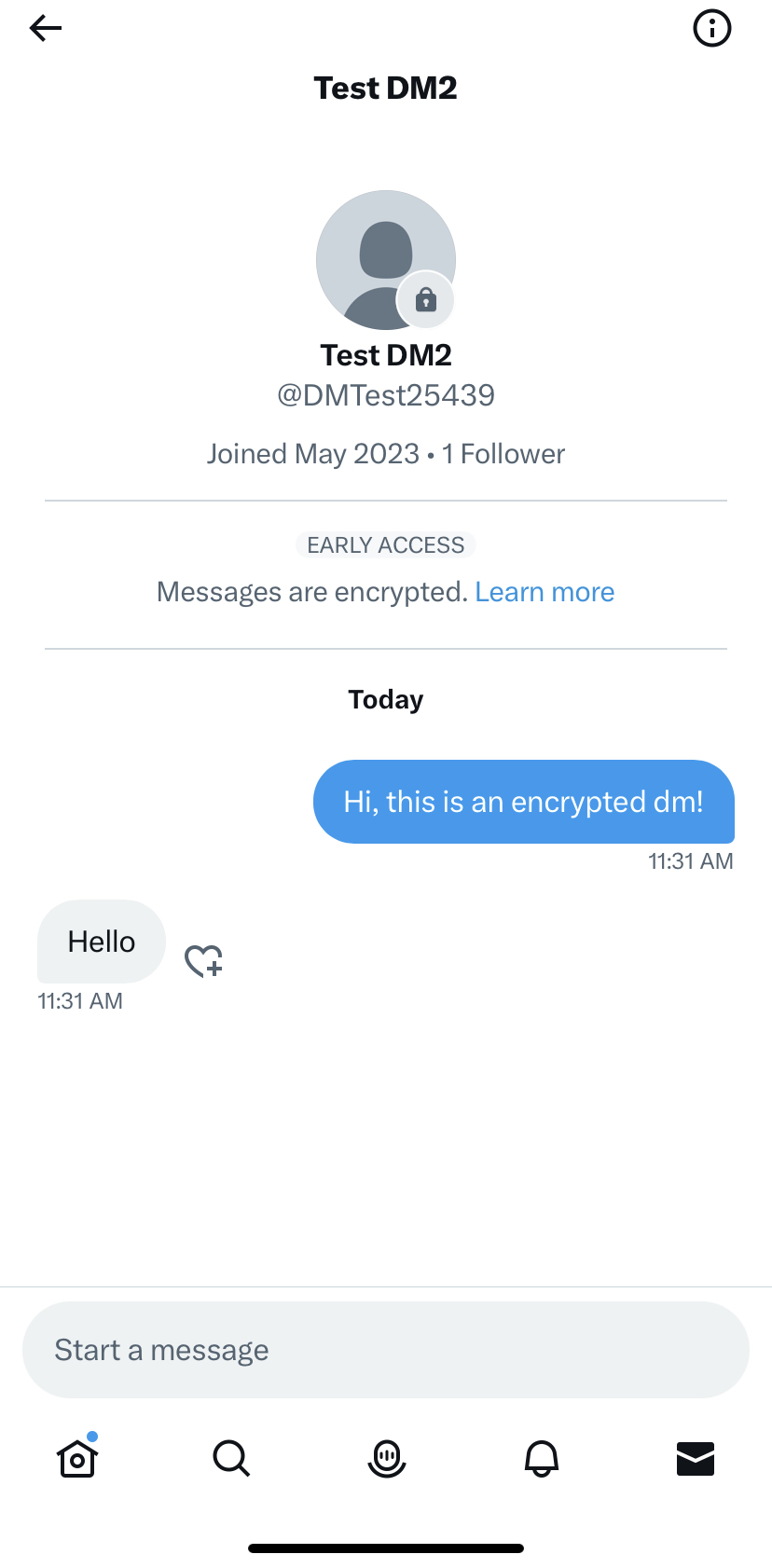
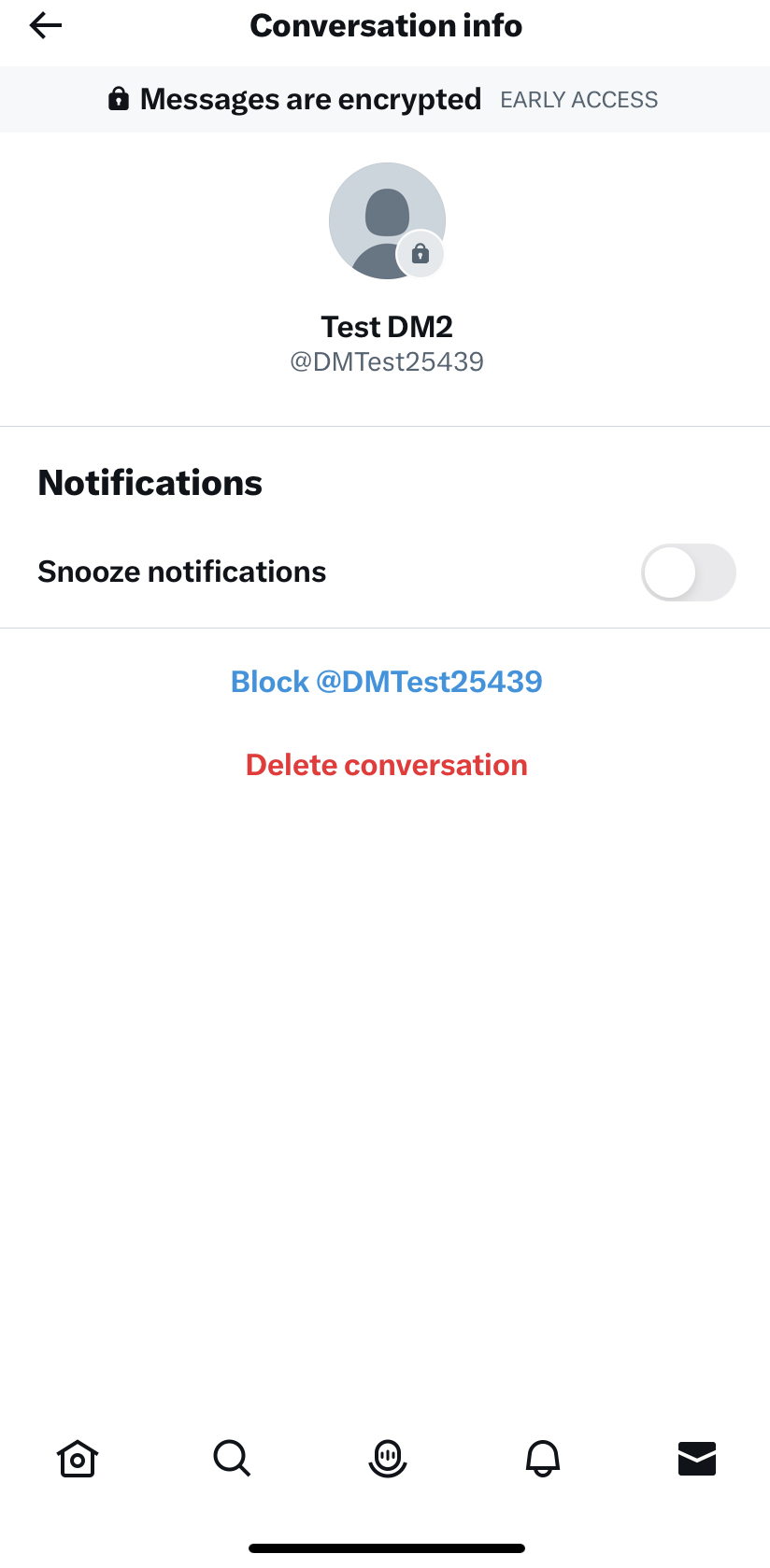
You can also check if a conversation is encrypted from the Conversation info page. The Conversation info page displays the following label at the top for encrypted conversations: “Messages are encrypted.”
Registration / Unregistration
A new device logged into X will get automatically registered for Encrypted DMs. You can check the list of your devices registered for Encrypted DMs via the Device List page:
Navigate to your inbox
Tap on settings icon on top right of the screen
Tap on Devices under “Encryption” header
We currently allow a maximum of ten devices per user for encrypted messages. After you have reached the limit, you will not be able to send and receive encrypted messages on any new devices that are logged into X.
You can manually unregister a device for Encrypted DMs from the Device List page:
Navigate to the Device List page
Identify and tap on the device you want to deregister
It can be the current device on which the deregistration or any other registered device belonging to the user
Tap on “Unregister this device”
Confirm the action.
Unregistering a device will lead to removal of Encrypted DMs history from that device. Also the unregistered device will no longer be able to receive any new Encrypted DMs that the user sends or receives on their other registered devices. If the user unregisters their only device registered for Encrypted DMs, then the user will lose access to their entire Encrypted DMs history but other participating users might still have access to the history.
Once a device is manually unregistered, the device will not be automatically re-registered. An unregistered device can be manually re-registered from the Device List page:
Navigate to the Device List page on the device that needs to be re-registered
Tap on the device under the “Current device” header
Tap on “Register this device”
Once a device is re-registered, it will be eligible to start and join new encrypted conversations but it won’t get back its original Encrypted DMs history. See here for more information.
Limitations
We welcome feedback and are actively working on improving every aspect of the product, from user experience to the protocol security by removing most of the following limitations.
Groups
For now, encrypted messages can only be sent to a single recipient. We’ll soon be expanding this feature to group conversations.
Content
An encrypted message can only include text and links; media and other attachments are not supported yet. When users attempt to send media via an encrypted conversation, this action will not be completed. Reactions to encrypted messages are also encrypted. Also, while messages themselves are encrypted, metadata (recipient, creation time, etc.) are not, and neither is any linked content (only links themselves, not any content they refer to, is encrypted).
New devices
Currently, new devices cannot join existing encrypted conversations. Existing encrypted conversations and the messages in the conversation will be filtered out on new devices that you log into. If you try to access an existing encrypted conversation on a new device via new message flow, it will show an error message indicating that the conversation is inaccessible on that device.
Note: a device will be considered a new device in the context of encrypted messages, if the X app is re-installed on the device.
Verify integrity of conversations
Currently, we do not offer protections against man-in-the-middle attacks. As a result, if someone–for example, a malicious insider, or X itself as a result of a compulsory legal process--were to compromise an encrypted conversation, neither the sender or receiver would know. We are, however, working on mechanisms for a future release that will:
allow devices to verify the authenticity of the content and origin of the message (via “signature checks”); and
allow a pair of users to verify the devices that have access to their encrypted conversation (via “safety numbers”)
When signature checks and safety numbers are implemented, man-in-the-middle attacks should be difficult, if not impossible, and both senders and recipients should be alerted in the event of an attack.
Reporting
Currently, it is not possible to report an encrypted message to X due to the encrypted nature of the conversation. It is important to highlight that at this phase encrypted DMs do not allow for media. If you encounter an issue with an encrypted conversation participant, we suggest you file a report about the account itself and our team will take a look.
To stop someone from sending you encrypted messages:
open the encrypted conversation between you and the participant you wish to block;
tap the information icon to open your Conversation info; and
at the bottom of the screen you have the option to block the account.
Logout and Key backup
If at any time you log out from X, all messages including encrypted messages on your current device will be deleted; this will not impact your other devices.
Currently, we don’t erase the private key from the device on logout. After logging in back on the same device, your device will be able to re-fetch and decrypt the encrypted conversations using the private key that the device had access to before logout. Once we offer the key backup feature, we will start erasing keys on logout. Until then users should exercise caution while using the product on a shared device such as public computers.
Forward Secrecy
If the private key of a registered device was compromised, an attacker would be able to decrypt all of the encrypted messages that were sent and received by that device. In other words, this implementation is not “forward secure”. Our customers expect their (unencrypted) DM history to be stored in the cloud and downloadable on any device that they are logged into. Unfortunately, this user experience doesn’t work well with forward secure messaging protocols. In order to preserve and extend this user experience to encrypted messages, we decided to forgo forward secrecy. We don’t plan to address this limitation.
Encrypted message deletion
Just like a Direct Message, when you delete an encrypted message, it is deleted from your account only, not from the other participant’s inbox. Deleting or leaving an encrypted conversation will not prevent the other person from sending you a Direct Message in the future.
When you delete an encrypted message or conversation (sent or received), the data will be instantly deleted from your device (and soon after from all your other devices). You then will no longer be able to view it. Note that the recipient may still be able to see the encrypted message or conversation you have deleted.
Questions?
Post us @XEng!